WHAT IS IT?
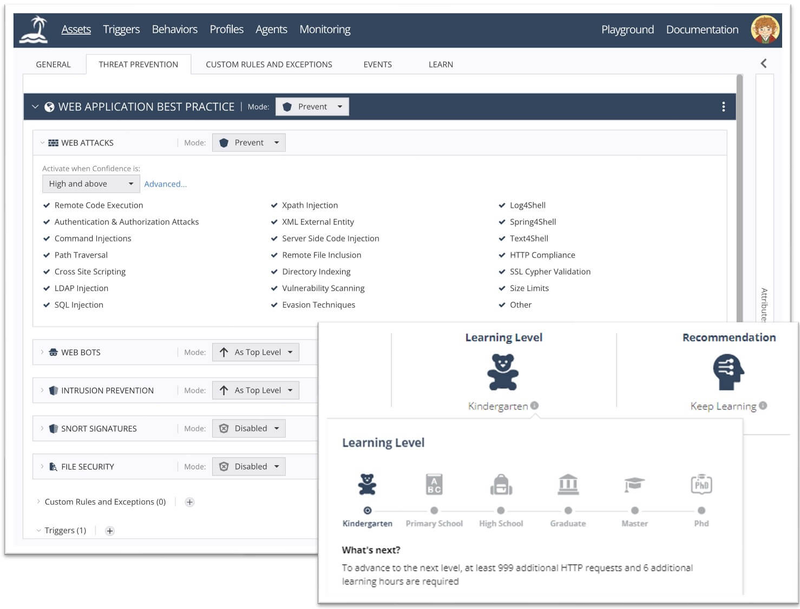
open-appsec is an application security engine (WAF/WAAP) that uses machine learning to automatically block attacks against web applications and APIs. Instead of maintaining hundreds of ModSecurity rules or CRS signatures, it analyzes request patterns in real time to detect OWASP Top-10 and zero-day attacks with no human tuning.
WHY IS IT INTERESTING?
- Two-stage ML approach: a supervised model trained on millions of requests flags suspicious traffic, then an unsupervised model learns your specific traffic profile to decide whether to block. This drastically reduces false positives.
- No rules to maintain: no CRS tuning, no signatures to update. The engine continuously learns from your traffic.
- Plugs into what you already run: native modules for NGINX, Kong, APISIX, Envoy/Istio. Deployable on Linux, Docker, or Kubernetes (official Helm chart).
- Genuinely open source: code and base ML model under Apache 2.0. An optional SaaS UI exists, but the engine runs standalone with plain config files.
- Audited: OpenSSF Best Practices badge, documented third-party security audits. That's rare for a young security project.
USE CASES
- Protect an NGINX or Kong reverse proxy in front of internal APIs without writing ModSecurity rules
- Add a WAAP layer to a Kubernetes cluster via the NGINX Ingress or Istio module
- Replace a proprietary cloud WAF (AWS WAF, Cloudflare) with a self-hosted, auditable alternative
- Shield exposed legacy applications when modifying their code is not an option